Ledger Cold Wallet Security: Complete Architecture Analysis
Ledger Cold Wallet Security represents a multi-layered protection system designed to isolate cryptocurrency private keys from all potential attack vectors present in connected computing environments.
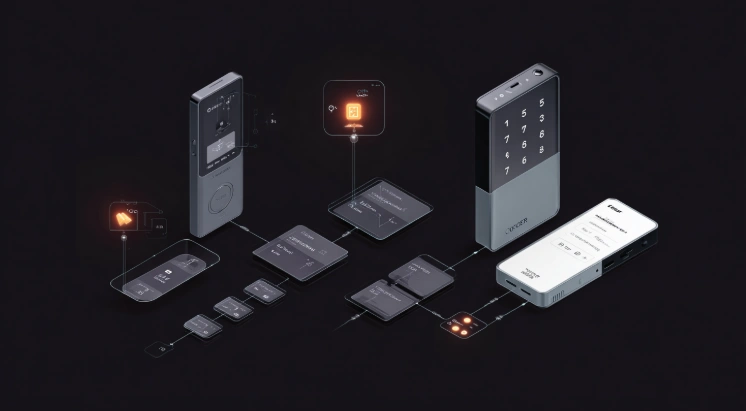
Ledger Cold Wallet Security represents a multi-layered protection system designed to isolate cryptocurrency private keys from all potential attack vectors present in connected computing environments. The security architecture combines certified hardware components, hardened firmware, and secure communication protocols to create comprehensive protection for digital assets. Understanding this architecture enables users to appreciate the depth of protection hardware wallets provide compared to software alternatives.
Ledger Cold Wallet Wallet Security and Ledger Cold Wallet Security Architecture reflect over a decade of development focused specifically on cryptocurrency protection requirements. The architecture addresses threats ranging from sophisticated malware to physical device attacks, providing cold storage security that adapts to evolving threat landscapes. Unlike software wallets running on general-purpose devices or competitors like Trezor and KeepKey with different architectural approaches, Ledger employs certified secure elements meeting banking and government security standards. This page provides comprehensive analysis of the security architecture protecting assets across all supported coins.
Security Architecture of Ledger Cold Wallet

Ledger cold wallet security and ledger cold wallet wallet security implement a defense-in-depth strategy where multiple independent security layers protect private keys from compromise. The architecture ensures that breaching any single layer does not provide access to protected keys. Each component serves specific security functions while integrating with others to create comprehensive protection for hardware wallet users.
The architecture separates security-critical operations from general functionality, ensuring that sensitive cryptographic operations occur exclusively within protected environments. This separation principle prevents exposure of private keys regardless of what occurs in less protected system components during cold storage operations.
Core Security Principles Behind Ledger Cold Wallet
Ledger cold wallet security principles fundamental to the architecture:
| Security Principle | Implementation | Protection Provided |
|---|---|---|
| Key isolation | Secure element chip | Keys never leave protected environment |
| Minimal attack surface | Dedicated firmware | Reduced vulnerability exposure |
| Physical verification | On-device display | Transaction manipulation prevention |
| Cryptographic integrity | Signed firmware | Unauthorized code prevention |
| Tamper resistance | Hardware protections | Physical attack deterrence |
| Zero trust design | Independent verification | No reliance on host security |
Each principle addresses specific threat categories while contributing to overall crypto security posture. The combination creates protection exceeding any single measure's capability.
Why Cold Wallets Provide Stronger Protection
Cold wallet security benefits compared to connected alternatives:
- Private keys never exist on internet-connected devices
- Malware cannot access keys stored in isolated hardware
- Phishing attacks cannot extract keys from secure elements
- Remote exploits cannot reach air-gapped key storage
- Physical confirmation prevents unauthorized transactions
- Hardware security exceeds software-only protection capabilities
- Dedicated devices reduce attack surface compared to general computers
Cold storage fundamentally changes the security model by eliminating network connectivity from the equation. Attacks requiring network access simply cannot reach properly isolated cold wallet systems via USB-C or Bluetooth when not connected.
Hardware Security Components

Ledger cold wallet security relies on specialized hardware components providing protection that software alone cannot achieve. The secure element chip forms the core of hardware protection, implementing cryptographic operations in a tamper-resistant environment certified to banking security standards. Additional hardware features complement secure element protection for comprehensive hardware security.
Hardware security differs from software security in providing physical guarantees rather than logical protections. Attackers must overcome physical barriers rather than simply finding software vulnerabilities, dramatically increasing attack difficulty and cost.
Secure Element Chip Technology
Ledger cold wallet security architecture secure element specifications. Secure element protection features:
- CC EAL5+ certified security rating
- Tamper-resistant physical construction
- Side-channel attack countermeasures
- Fault injection protection
- Encrypted key storage
- True random number generation
- Cryptographic acceleration hardware
- Physical memory protection
- Secure boot verification
- Anti-cloning mechanisms
The secure element provides protection equivalent to chip technology in credit cards, passports, and secure ID systems. This proven approach addresses real-world attack scenarios rather than theoretical threats across all supported coins.
Software Security Layers

Ledger cold wallet wallet security extends beyond hardware to include firmware and software layers that complement physical protections. The software stack implements security policies, manages communication protocols, and provides user interfaces while maintaining separation from security-critical operations. Each software layer undergoes security review and testing to ensure consistent protection.
Software security works together with hardware security rather than replacing it. The combination provides defense-in-depth where multiple barriers must be overcome for successful attacks against cold storage systems.
Firmware and Application Security
Ledger cold wallet security software protections:
| Security Layer | Function | Verification Method |
|---|---|---|
| Secure boot | Prevents unauthorized code execution | Cryptographic signature check |
| Firmware integrity | Ensures code authenticity | Hash verification |
| Application isolation | Separates blockchain apps | Memory protection |
| Secure communication | Protects device-host traffic | Encrypted channel |
| Genuine check | Confirms device authenticity | Server attestation |
Firmware updates undergo cryptographic verification before installation, preventing attackers from loading malicious code even with physical device access. Unlike Trezor or KeepKey with different software architectures, Ledger maintains strict firmware security protocols.
For private keys protection, see our Ledger Cold Wallet Private Keys guide. For phishing protection, visit Ledger Cold Wallet Phishing Protection. For safety review, see Is Ledger Cold Wallet Safe.
Frequently Asked Questions
-
Hardware isolation keeps private keys in secure elements that never connect to networks. Software wallets store keys on internet-connected devices where malware can access them.
-
Yes. Ledger uses CC EAL5+ certified secure elements verified by ANSSI (French National Cybersecurity Agency). This certification requires independent security evaluation.
-
No successful attacks extracting private keys from Ledger secure elements have been publicly documented despite significant research efforts and bounty programs.
-
Private keys generate inside the secure element and never leave it. All cryptographic operations occur within the protected chip, preventing key exposure.
-
No. Connection types transport only transaction data and signatures. Private keys remain in the secure element regardless of connection method for cold storage protection.
-
Without the PIN, thieves cannot access wallet functions. After three incorrect attempts, the device wipes. Assets remain accessible via recovery phrase on replacement devices.
-
Ledger uses certified secure elements while some competitors use general-purpose microcontrollers. All hardware wallets dramatically exceed software wallet security.